Clean Slate
Site B - Attack/Defend Scenario
Mission Briefing

Administrator Jayanti
The Evolved Intelligence has taken our bait, Commander. Their dropships de-orbit on the secure complex as we speak, and the Coalition Navy reports unusual orbital movement over the site. Your colleagues on the ground are going to endure much suffering to sell this ruse.
However, it is important that we keep the ruse from sliding into an actual catastrophe. While we must regretfully cede ground to the enemy, it cannot be to the degree where they see us as a trivial foe whom they can rob without consequence. They must learn that attacking us has a price, lest they be emboldened and reach greedily for more.
This is not mere idle philosophy, Commander. Already the Evolved Intelligence has foreseen its victory, and assumes to claim further prizes. While its heavy forces descend on the contraband, an infiltration team has just tripped alarms at the Airavata data hub in the heart of Silvania. This is bold even for the Combined Army-- Airavata is no mere routing node. One third of all Maya traffic and half of all ALEPH processing on Paradiso passes through here. ALEPH's tracking of the Evolved Intelligence's intrusion into Maya hinted that it had some interest in the site, but we never guessed that it would attack such a well-fortified hub so brazenly.
It is unclear what the Intelligence aims to accomplish once inside Airavata, but several alarming possibilities exist. The facility is a control hub for Ghost-linked remotes on the entire Norstralian continent, as well as a data repository for trillions of Maya termi
This infiltration indicates an alarmingly cavalier level of confidence in our foe. If it believes itself free to divert resources from its primary goal to casually harass our informational infrastructure, that tells us that we are already losing credibility in its eyes as a foe.
Mission Briefing

Noctifer-Agent Keeskreet
This whole distasteful mess will soon be over, Commander. I have just been given the order to organize the final and most crucial step in the Unfolding Intellect's great scheme, and because you have proven your worth as a subtle operator, I have recommended you to execute it.
The final stolen samples will soon be reduced to sparkling dust, but this annihilation serves little purpose if the humans are permitted to keep the intelligence furnished to them by the traitorous Exrah. They have held the master's works before and will obtain more in the future, but these wonders are so vastely beyond the understanding of their pitiful mammal brains that we need not worry. Let them bash their rocks against our weapons, it will do them no good.
This is different, however. The Exrah fiends sold the humans not only technology that was not theirs to barter, but also the knowledge of how to employ it. This, the Intellect cannot tolerate. And so you will be performing the most crucial task of this entire campaign: you will slice into the human data networks and expunge all traces of the Exrah data. An undertaking this vast cannot be performed from just any access point in their network, however; you must stand within a central junction of their datastream, from where you may view all corners of their knowledge net and burn away the pieces that they do not deserve.
This task is the most vital you will ever be asked to perform, Commander. If the humans are permitted to wield the power of the Intellect's devices without submitting to its will, that will undermine the great sacrifice of all those of us who have given up our racial destinies to serve. This insult cannot be suffered.
Succeed, and the eyes of a grateful god will be upon you.
Be safe, Commander.
...
Hmm? Oh, right, the other matter.
Did you see those monkeys grunting off toward the hangar? They've volunteered to march directly into the gunfire of the humans protecting the last dregs of the Exrah contraband, in the hopes that the Unfolding Intellect will favor one frothing horde of knuckle-dragging primates over another in the aftermath.
Your assessment is correct: they are morons.
The Intellect agrees with my analysis that their plan is doomed and the monkeys are all going to get butchered. Unfortunately, the Intellect and I begin to diverge slightly on the matter of whether or not that would be a good thing. The wisdom of the Intellect is truly inscrutable to we mere mortals, as it has for some reason determined that measures should be taken to ensure that a few of them survive their suicidal charge.
So while you're inside the enemy data stream, see if you can locate the human machine logic subroutines for the devices they've have layered around their stolen prize. It should be a simple matter to turn the crude devices away from our illustrious allies and toward their masters.
Do so, and you will have the thanks of a belching red stench cloud. Truly, a prize to be envied.
Mission Objectives
Special: Achievement of mission objectives during the mega-battle directly awards League Points.
Attacker (Combined Army)
- 2 Delete the Data
Defender (Human Coalition)
- 1 Preserve the Data
Terrain
- An ALEPH data core.
- Indoors: This mission takes place indoors. Models with AD Lv3 or higher cannot deploy by combat jump, though they may downgrade to AD Lv2: Airborne Infiltration.
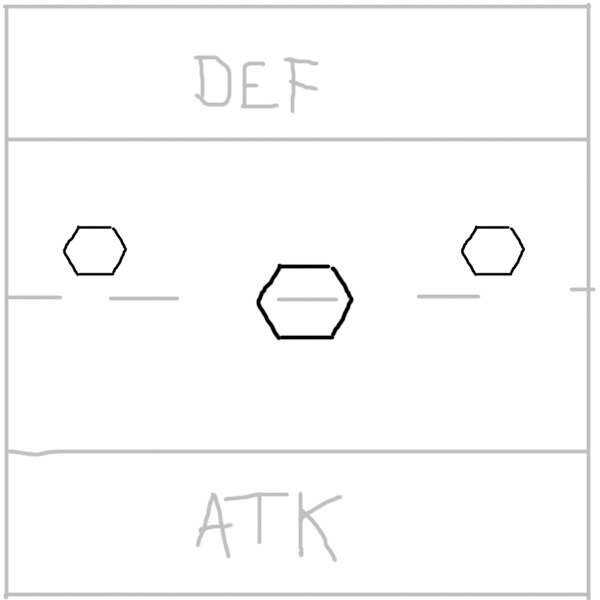
Deployment & Setup
-
Before the Initiative Roll is made, after both players have chosen their Army Lists, place the following as indicated on the map above:
- Three Fulcra (FUL)
- Three Defensive Turrets. These turrets must be placed by the Defending player, and may be placed anywhere outside of both players' deployment zones.
- Both players will deploy on opposite sides of the game table, in a standard Deployment Zone 12 inches deep.
Scenario Note
A hacker within a Fulcrum has access to the Puppeteer program, which enables possession of Defensive Turrets. Two can be possessed at once if they are placed within 12" of each other.
Special Rules & Objectives
- Fulcra: The facility's network is primarily accessed through three Data Fulcra. A hacker may take control of a Fulcrum by succeeding on a WIP+3 roll while standing within it. On a failure, the roll may be reattempted as many times as necessary, spending the corresponding short skill each time.
- Wide Net Hack: At the end of each Game Round, if any Fulcrum Hacking Programs have successfully generated effects on other tables, the effects of those programs are resolved.
- Deleting the Data: The Evolved Intelligence demands that the human research data be completely excised. Each success by the Attacker's hackers on the SCOUR hacking program will locate and destroy one third of the data. Once the Attacker has succeeded on this program three times, the data will be considered to have been completely Deleted.
- Preserving the Data: The captured research data is extraordinarily complex, and will become too difficult to decode if too much of it is lost. At the end of the game, if the Attacker has succeeded no more than once on the SCOUR hacking program, the data will be considered to have been Preserved.
-
Defensive Turrets: At the start of the game, the Defending players must deploy three Defensive Turrets around the board. All Defensive Turrets have the following profile:
REM
(Hackable)Adhesive Turret BS WIP STR ARM BTS 11 13 1 3 3 Abilities: Total Reaction, G:Remote Presence Equipment: 360 Visor, Multispectral Visor Lv.1 Weapons: Adhesive Carbine*, Electric Pulse Special Adhesive Carbine
DMG Burst Ammo Properties - 2 Adhesive Non-Lethal 0-8 8-16 16-24 24-32 32-48 +6 0 -3 - -
REM
(Hackable)Ghost Turret BS WIP STR ARM BTS 11 13 1 1 6 Abilities: G:Remote Presence Equipment: 360 Visor, Automated Hacking Device, ODD Weapons: Electric Pulse Special: Automated Hacking Device: This model's Hacking Device has access to the following programs:
- CLAW-1: Gotcha!
- CLAW-1: Oblivion
- CLAW-1: Overlord
- SHIELD-2: Breakwater
- UPGRADE: White Noise
Sentry Turrets begin the game friendly to the Defending Player. They do not receive an Active Turn, but may perform AROs against enemy models.
- Nullification Protocol: ALEPH protects its data cores with an advanced jamming field which infiltrates and disables the driving logic of hostile equipment and competing networks within its environs. As a result of this interference, all models with G: Remote Presence within the facility become Irregular. Additionally, at the end of each Player Turn, all deployable equipment and deployable weapons on the board are disabled.
While controlling a Fulcrum, a Hacker's BTS becomes 9, and it gains access to a number of special Hacking Programs, which are listed in the appendix at the bottom of the scenario description.
Appendix: Fulcrum Hacking Programs
- The following Hacking Programs are available to any Hacker within a Fulcrum.
- Each of these programs is limited for each player to one success per Game Round that has occurred. If no successes are earned during a particular Game Round, that round's eligible success is passed to later rounds. E.g., if the Attacker tries and fails to SCOUR during Game Round 1, he may succeed up to twice during Game Round 2, but may not score a third success until Game Round 3.
- Many of the programs can be used to affect the other Mission Sites. Any effects generated on other boards will be resolved at the end of the Game Round during Wide Net Hacking.
SCOUR
GADGET-3
REQUIREMENTS
- This program may only succeed once for each Game Round that has occurred.
EFFECTS
- In the Active Turn, the user must succeed on a WIP-3 roll.
- On a successful roll, 1/3 of the human research data is located and deleted.
- Once this program has been accomplished three times, the Combined Army will be considered to have Deleted the Data.
PUPPETEER
Attack, CLAW-3
REQUIREMENTS
- The target must be up to two enemy Defensive Turrets at any Battle Site, both of which must be within 12" of each other.
- This program may only succeed once for each Game Round that has occurred.
EFFECTS
- In the Active Turn, the user must succeed on a WIP roll. The target is not eligible for a Reset ARO.
- Each successful Roll forces the target to make a BTS Roll vs Damage 16.
- Failing the BTS Roll causes the target to enter the Possessed state, signified by a Possessed Marker (POS)
- Unlike a possessed TAG, a possessed Defensive Turret's stats are not altered.
- A possessed Defensive Turret may be freed of its status in the same way as a possessed TAG, or it may be targeted with this program by another player cancel its current Possession and assign it a new controller.
SABOTAGE
Attack, GADGET-3
REQUIREMENTS
- The target must be a Conduit at Site C.
- This program may only succeed once for each Game Round that has occurred.
EFFECTS
- In the Active Turn, the user must succeed on a WIP roll. The target is not eligible for a Reset ARO.
- On a successful roll, choose one:
- the targeted Conduit is Disabled, signified by a Disabled Marker (DIS).
- the targeted Conduit is no longer Disabled. Remove its Disabled Marker (DIS). Note that this program cannot repair a Conduit that has actually been Destroyed.
- While Disabled, the targeted Conduit behaves in the same way as if it had been Destroyed.
- This Disabled state may be cancelled through a subsequent use of this same program, or by having an Engineer or Hacker in base contact with the Disabled Conduit succeed on a normal WIP Roll.
UNSEAL
GADGET-3
REQUIREMENTS
- The target must be either:
- one or two locked door within 12" of each other at any mission Site; or,
- one room with multiple locked doors at any mission Site.
- This program may only succeed once for each Game Round that has occurred.
EFFECTS
- In the Active Turn, the user must succeed on a WIP roll.
- On a successful roll, the targeted door is unlocked. If the target is an objective room with multiple entrances, all of its doors become unlocked.
IMPEDE
SHIELD-3
REQUIREMENTS
- None.
EFFECTS
- In the Active Turn, the user must succeed on a WIP roll.
- On a successful roll, the user enters the BLOCK state.
- While in this state, the user automatically applies a cumulative -3 penalty to all enemy hacking attempts made from within a Fulcrum, except rolls to activate the IMPEDE program.
- This state is automatically cancelled at the end of the current Game Round, when the user leaves its Fulcrum, or when the user performs any other hacking program.
 Print
Print